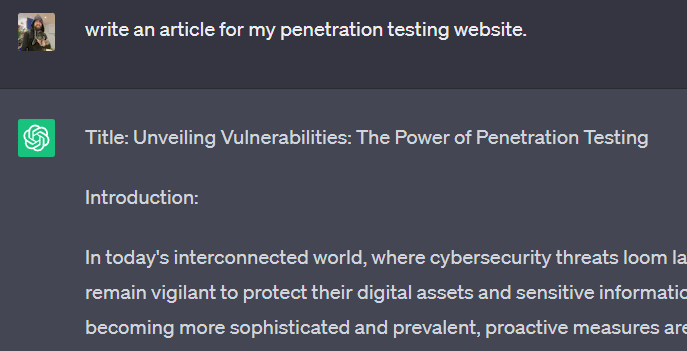
Human prompt: “write an article for my penetration testing website”
Human paragraph:
I need content for my website, not just for you, but for me. See, I won’t get good Search Engine Optimization (SEO) results unless I have content on my site. But guess what? The content I write is too abstract and technical for the common audience and as a result SEO scores will suffer. This means, as a business owner, that I don’t get search results unless I push fluff to my website. That fluff shows up in search engines, and increases my ad successes.
I don’t want to write fluff, but in order to successfully market myself, technology says I have to. So enjoy this relevant article (it actually is relevant content, it’s just grossly overwritten and already covered material) entirely written off of a single prompt to ChatGPT. Its a great summation of the services that I offer. If you need these services, feel free to contact me, below is exactly what I do.
Introduction:
In today’s interconnected world, where cybersecurity threats loom large, organizations must remain vigilant to protect their digital assets and sensitive information. With cyberattacks becoming more sophisticated and prevalent, proactive measures are essential to stay one step ahead of potential threats. Enter penetration testing, a critical component of any robust cybersecurity strategy. In this article, we will explore the significance of penetration testing and how it helps organizations identify and address vulnerabilities before malicious actors exploit them.
Defining Penetration Testing
Penetration testing, also known as ethical hacking or pen testing, is a systematic process of simulating real-world cyberattacks on an organization’s network, systems, or applications. It involves authorized security experts attempting to breach defenses, uncover weaknesses, and gain unauthorized access to assess an organization’s security posture. This process aims to identify vulnerabilities and help organizations fortify their security measures.
The Objectives of Penetration Testing
Penetration testing serves multiple purposes, all geared towards enhancing an organization’s security posture:
a. Identifying Vulnerabilities: By simulating real-world attacks, penetration testers aim to identify weaknesses in networks, systems, and applications. This includes software vulnerabilities, misconfigurations, weak passwords, and other potential entry points for cybercriminals.
b. Assessing Defense Mechanisms: Penetration testing evaluates an organization’s existing security controls, such as firewalls, intrusion detection systems, and access controls. By doing so, it helps organizations gauge the effectiveness of their defenses and identify areas that require improvement.
c. Testing Incident Response: Penetration testing can also evaluate an organization’s incident response capabilities. By simulating an attack, testers can assess how well the organization detects, responds, and mitigates potential threats.
d. Compliance and Regulations: Penetration testing helps organizations meet regulatory requirements, such as those outlined by industry standards like the Payment Card Industry Data Security Standard (PCI DSS) or the General Data Protection Regulation (GDPR).

The Penetration Testing Process
Penetration testing typically follows a well-defined process to ensure comprehensive coverage and accurate results:
a. Planning and Reconnaissance: This phase involves gathering information about the target organization, including its infrastructure, systems, applications, and potential vulnerabilities.
b. Scanning and Enumeration: Testers employ various tools and techniques to scan the target systems, identifying open ports, services, and potential entry points.
c. Exploitation: In this phase, testers attempt to exploit identified vulnerabilities to gain unauthorized access, escalate privileges, or execute specific attack scenarios.
d. Post-Exploitation and Analysis: Once access is gained, testers assess the extent of the compromise and evaluate the potential impact on the organization’s systems and data.
e. Reporting: The final phase involves documenting the findings, including identified vulnerabilities, potential risks, and recommendations for remediation. A comprehensive report helps organizations understand the vulnerabilities discovered and prioritize their remediation efforts.
Benefits of Penetration Testing
Investing in regular penetration testing provides numerous benefits to organizations, including:
a. Risk Mitigation: By proactively identifying vulnerabilities, organizations can address them before cybercriminals exploit them, significantly reducing the risk of successful attacks.
b. Enhanced Security Awareness: Penetration testing increases awareness among employees regarding potential security threats and the importance of adhering to security policies and best practices.
c. Regulatory Compliance: Many industry regulations require periodic penetration testing as a mandatory security measure. Conducting these tests ensures compliance and helps avoid penalties.
d. Cost Savings: Detecting and fixing vulnerabilities during the testing phase is far less expensive than dealing with the aftermath of a successful cyberattack, including potential legal fees, reputational damage, and financial losses.

Conclusion:
In an increasingly digital landscape, where the stakes of a cyberattack are higher than ever, penetration testing serves as a crucial tool to safeguard organizations’ sensitive data and assets. By proactively identifying vulnerabilities and weaknesses, penetration testing empowers organizations to fortify their defenses, enhance their incident response capabilities, and stay ahead of potential threats. Embracing penetration testing as a regular security practice is not just a wise investment but a critical step towards maintaining a robust cybersecurity posture in today’s ever-evolving threat landscape.
